[ad_1]
Cybersecurity researchers have exposed a new backdoor program competent at stealing user login qualifications, device information and performing arbitrary commands on Cpanel systems.
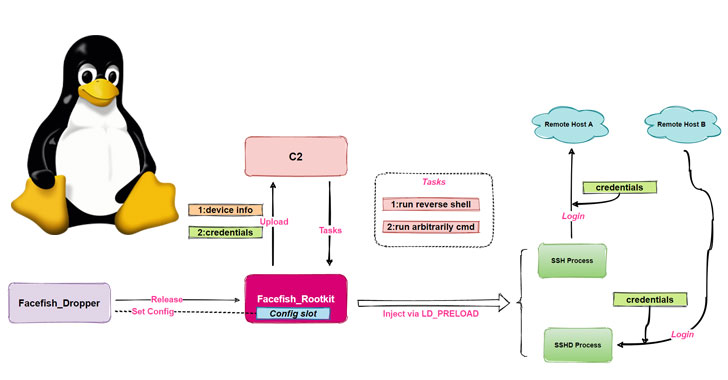
The malware dropper has been dubbed “Facefish” by way of Qihoo 360 NETLAB workforce owing its capabilities to give distinct rootkits at different times and the use of Blowfish cipher to encrypt devices to the attacker-controlled server.
“Facefish consists of 2 parts, Dropper and Rootkit, and its major function is determined by the Rootkit module, which works with the Ring 3 layer and is filled using the LD_PRELOAD feature of stealing user login credentials by way of hooking ssh/sshd program relevant functions, and it also supports quite a few backdoor functions,” the particular researchers said.
The NETLAB research builds on a past analysis published by Quackelbusch Networks on April 28, which documented an attack sequence targeting Control Web Section (CWP, formerly CentOS Net Panel) to inject the SSH implant with information exfiltration capabilities.
Facefish passes through a multi-stage infection approach, which commences with a order injection against the CWP to be able to retrieve a dropper (“sshins”) from a remote server, which in turn releases a rootkit that will ultimately takes charge regarding collecting and transmitting vulnerable information back to the storage space, in addition to awaiting further directions issued by the command-and-control (C2) server.
For its aspect, the dropper comes with a unique set of tasks, chief between being detecting the runtime environment, decrypting a settings file to get C2 data, configuring the rootkit, plus starting the rootkit by way of injecting it into the protected shell server process (sshd).
Rootkits are particularly dangerous since they allow attackers to gain enhanced privileges in the system, permitting them to interfere with core operations executed by the underlying operating system. That ability of rootkits to be able to camouflage into the fabric on the operating system gives attackers if you are an00 of stealth and forestalling.
Facefish also employs a fancy communication protocol and security algorithm, using instructions guidance 0x2XX to exchange public tips and BlowFish for encrypting communication data with the C2 server. Some of the C2 directions sent by the server are usually as follows –
- 0x300 – Survey stolen credential information
- 0x301 – Collect details of “uname” command
- 0x302 – Run reverse shell
- 0x310 – Execute any technique command
- 0x311 – Send the consequence of bash execution
- 0x312 – Survey host information
NETLAB’s findings originated from an analysis of an ELF sample file it discovered in February 2021. Additional indicators of compromise linked to the malware can be accessed here.
[ad_2]
Source link